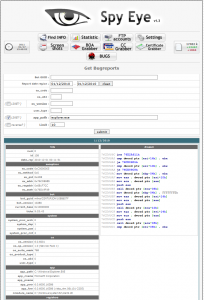
In my day-to-day work, I focus quite heavily on the configuration files and the way trojans work in a particular circumstance.
Spyeye is obviously one of the trojans that is high on the radar as it is believed that the authors behind Zeus and Spyeye have “merged”. This has been supported by findings that Zeus and Spyeye trojans can now talk to the same backend system. (All trojans need a C&C server where they report their stolen data to. In this case, the C&C backend can handle data from Zeus and Spyeye).
The Spyeye trojan has a plugin structure that is extensible and makes sure that the trojan can adapt to new situations.
Well known Plugins are:
- webfakes (alter web content in HTTP and HTTPS requests… this is to compromise any website)
- ddos (denial of service)
- ccgrabber (credit card grabber… scans POST request for credit card numbers (using Luhns algorithm) and steals the info)
- backconnect (either via RDP or SOCKS5. provides a means for the fraudster to connect to your computer)
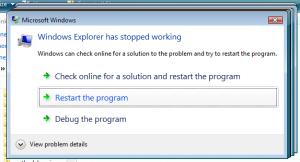
But one plugin was new to me
- bugreport
This plugin takes care of any crashes of the Spyeye trojan and more details to the problem will be sent to the fraudster. The fraudster can also define what should happen in this case.
WOW… A built-in mechanism that allows the perpetrators to collect critical QA information from client systems to help them to make the trojan better? How many commercial software applications do have a similar system?