One of the questions that always comes up at conferences and discussions is “how exactly get people infected with malware?”. The funny thing is that we malware researcher deal with this on a day-by-day basis, and the obvious reply ranges from malicious ad-banners to infected homepages/drive-by-downloads and phishing. All these techniques unfortunately work great.
One technique that is always a bit overlooked are malicious emails due to the “perception” that spam filters are effective. (whatever that means – especially in light of the RSA attack where the initial payload was an email which ended up in the spam folder and people moved it to the inbox to execute the attachment!!!). And my spam filter typically works really, really well…
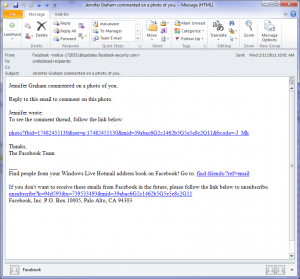
Well, the other day I received an email from facebook that someone commented on a photo of myself
The interesting fact was that this email wasn’t in my spam folder, but rather in my inbox. Being one of the over 800 million facebook users, I thought: cool… let’s check it out and clicking on this link straight away downloaded a file called “FBviewer.exe”… Yeah, facebook viewer… makes sense.
Unsurprisingly this doesn’t smell right, so I asked virustotal what all the AV engines think of this file. As it turnes out, not much. 3 out of 43 AV engines detect something. Two with a heuristic (which may well be a false positive as well) and one AV detects something, but something completely wrong. The VT link is here: http://www.virustotal.com/file-scan/report.html?id=a34587d5bb473761ad9deb406dbc7515815325ca98d896238b696adf339b43cb-1320717477.
The disturbing fact is that none of the big AV engines detected this, so the “real” detection rate is close to zero.
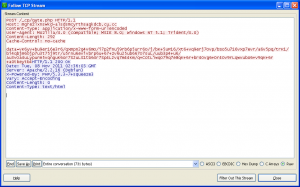
I’ve no idea how Avast thinks this is Carberp, because this is a Spyeye trojan. When we analyzed the trojan, the C&C server was obviously still active, but luckily didn’t reply with a configuration files, so this instance of my Spyeye trojan was instructed to do nothing.
In conclusion, this was almost a perfect storm. A fairly well written email that made it past the spam filter with a convincing topic that most people would fall for. The download of a trojan with virtually zero detection rate and probably a fairly high hit rate because people really want to find out what’s happening with this photo.
Luckily the trojan didn’t do anything on our system, but hey once you are owned, you are owned.