Executive Summary
In our last in-depth report we looked at enhancements of the notorious Zeus trojan that focus solely on making life harder for automated detection tools and tracking software. We looked at three variants that are based on the leaked source code. The fear is that a proliferation of too many different variant will make life harder to detect and track the various trojans.
One of the variants is called IceIx and on October 13 we noticed the presence of a new in-the-wild IceIx Zeus variant. We therefore decided to take a brief look. The sample had a size of 169,984 bytes and an MD5 of ed34b46a4524c7d05e45200eaf09f765. It contained exactly the same number of routines at the previous variant, 634. There were minor changes to around 20 of the routines, the rest were unchanged.
As you’ll see below, the changes are minimal, but the result is that all automatic decyrption routines will fail!
Well, it seems that the bad guys continue to “tweak” the encryption algorithm and the arms race continues up until we finally implement some proactive solutions rather than reactive countermeasures.
RC4 Variant
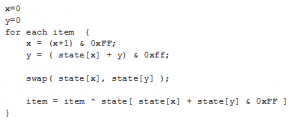
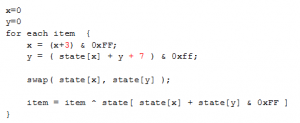
This version of Zeus is very similar to the initial ICE IX release, but has the RC4 algorithm tweaked. In the standard algorithm, a 256 byte ‘state’ table is initialised with the RC4 key, and the data is then decrypted as follows.
The modified algorithm changed the way the x and y values are altered.
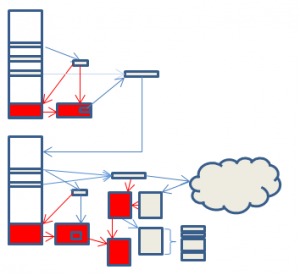
The areas affected in the decryption process are indicated in red in the diagram (please see our previous paper[1] for an explanation of the processes).
Although the areas affected seem extensive, in fact only a trivial change is needed to the rc4 algorithm for a security researcher to be able to decrypt the configuration file.
Notes on altering a Cryptographic Algorithm
For a layman to alter a cryptographic algorithm is usually bad. Seemingly trivial changes may introduce flaws that a cryptographer can exploit, and the chances are that the resulting output may be less resistant to cryptographic attack.
For a Zeus author, a slight lessening of cryptographic resistance probably does not matter. After all, the key and algorithm is provided with the Zeus source anyway. The end goal is to make life harder for a malware analyst, not a cryptographer, and so in this case the trade off is presumably acceptable to the author.
Configuration file download
The previous variant added extra parameters, ‘id’ and ‘hash’ to the HTTP command used to get the configuration data. This version changes the names of the parameters to ‘bn’ and ‘sk’.
The configuration file available at the ZeusTracker site has a version number 0×01010500.
Botnet
The botnet name used by this variant is rotewa11.
Summary
It seems as though this Zeus author has found at least one buyer even though his changes to Zeus are minor. Is seems that advertising does pay, even for malware.
This is the first time we have seen a Zeus variant using and altered version of a standard cryptographic algorithm, although no doubt it will not be the last.
[1] http://www.trustdefender.com/zeus-trojan-update-new-variants-based-on-leaked-zeus-source-code.html